Free digital signing of documents under Linux - an impossibility?
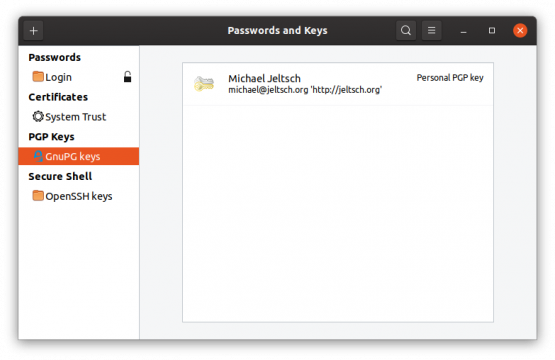
The whole story started when I tried to sign a LibreOffice document. When you belive the internet, document signing is inbuilt into LibreOffice. I still have to find the person that managed to digitally sign a LibreOffice document. This experience shows, that despite Edward Snowden most people do not proactively care about security and privacy. Debian removed scdaemon from the gnupg2 package and as usual, one needs to be a command line ninja to fix this. The scdaemon gives smartcard support (which I do not have, but without the scdaemon the Kleopatra key manager refuses to run). I am using the default Ubuntu 18.04 installation and it was quite an odyssey to get a document signed. In fact, I still do not have a satisfactory way to do this. However one does it, something's not right. Ubuntu 19.10 has fixed at least the invokation of the key manager from LibreOffice and I can invoke SeaHorse from the document signing dialog, but I still have no clue how to make my gpg keys visible to LibreOffice. Anybody figured this out? Until somebody shows me how to sign with LibreOffice, I use the very good, but proprietary software PDFStudio to import my GPG keys and sign my PDF files.
Signing services (DocuSign, HelloSign)
So what do you do if you need to sign e.g. a PDF and you have no means or do not want to subscribe to one of the document-signing certificate service like DocuSign? Even with DocuSign's budget plan a single digital signing costs $2. DocuSign has a 30-day free trial, but I do not know whether the certificats that you generate during the trial with continue to be valid after the end of the trial. HelloSign (https://www.hellosign.com, now owned by DropBox) has also a free tier (allowing to sign 3 documents/month) and when signing, it embeds an invisible signature (which was invalid for some strange reason when I tested it even though HelloSign is in Adobe's approved trust list).
Self-signing, cacert and StartSSL
Technically you can created your own signatures (self-signed certificates), but if such PDFs are viewed with Acrobat Reader, the signature will be flagged as invalid and the fact of self-signing is displayed. There used to be http://www.cacert.org/, but to my knowledge, all browsers have removed the CAcert certificates and the same is likely true for Acrobat. StartSSL used to give out free certificates, but they do not exist anymore (they were seriously challenged with their own security).
PDF Viewer support
Interestingly many PDF Viewers do anyway ignore the signing (e.g. the inbuilt PDF viewer from Firefox does not display anything). Other PDF viewers will display the signature, but NOT indicate, that it is not trusted (e.g. the Chrome Browser's PDF viewer and Ubuntu's default PDF viewer Evince). Since you have no idea what viewer your target will use to display your signed PDF, you are anyway in a bad situation (even if you subscribe to a document signing service).
Letsencrypt
To increase the trust in the signing, one can use a Letsencrypt certificate for signing. This signature certifies that the author of the document controls a specific website (in my case jeltsch.org). That is more than a self-signed certificate (and if the website is trusted, this is arguably also more than buying a subscription from DocuSign), but the re-purposed Letsencrypt certificate is not being trusted by Adobe since obviously the Letsencrypt endeavor was never meant for document signing ("Signer's identity is unknown because it has not been included in your list oif trusted certificates and none of its parent certificates are trusted certificats"). However, the maximum lifetime of such a certificate is 3 months, after which it becomes invalid. It can still be used, but it will display that it is not valid because it has expired (or is not valid yet).
How to misuse the Letsencrypt certificate
First, you need a web server, that uses Letsencrypt certificates to verify the web site identity. This is out-of-scope for this blog post, but there are several good tutorials (e.g. from the Let's Encrypt people themselves or from Digital Ocean). Once you have your Let's Encrypt certificates, this is the process to "misuse" them for signing documents:
Since Letsencrypt requires certificate renewal every three months, there will be lots of fullchain.pem and privkey.pem files in the same directory and they are numbered. You obviously want to use the newest (the only valid) certificate and perhaps you want to renew the Let's Encrypt certificate immediately before exporting it for document signing:
certbot --apache --force-renewal -n -d jeltsch.org or if you want to renew all certificates: certbot --apache --force-renewal If you choose to renew all certificates, certbot will try to issue a single certificate for all domains that exist on your server (this possibility did not exist in the beginning of the Letsencrypt ecosystem, but was introduced later). If your server serves more than one domain, you need to manually specify the domain name, for which you want the certificate.
For more details about how to use the certbot script, see https://certbot.eff.org/docs/using.html#certbot-commands
This is the command, that converts the certs into a PKCS#12 file:
openssl pkcs12 -export -out signing_certificat.p12 -in /etc/letsencrypt/archive/website-name/fullchain1.pem -inkey /etc/letsencrypt/archive/website-name/privkey1.pem
The PKCS#12 file stores the certificate and the private key in one encrypted file (with the file extension .p12). Therefore, the command will ask from you a keyphrase, which you absolutely need to remember to be able to use the certificate. Then you can transfer the p12 file to your desktop computer and use it to sign PDF files.
Time stamping servers
If your PDF application asks for a time stamping server, you can use one of the free services, e.g. ca.signFiles.com/TSAServer.aspx or http://zeitstempel.dfn.de. However, also these time stamping services are not trusted by Adobe Acrobat.
Here the commands to generate a self-signed certificate (it asks for a (temporary) passphrase, just make up something and remember it, you need it in the second step):
openssl req -x509 -newkey rsa:4096 -keyout key.pem -out cert.pem -days 3650
Conversion into a signing certificate (it first asks you for the temporary passphrase from above and then for the final passphrase, which you need to remember in order to use the certificate:
openssl pkcs12 -export -out signing_certificat.p12 -in cert.pem -inkey key.pem



